Breach的問題,我們搜遍了碩博士論文和台灣出版的書籍,推薦Greenberg, Slava寫的 Animated Film and Disability: Cripping Spectatorship 和Brassell, Andy的 Football Murals: A Celebration of Soccer’’s Greatest Street Art都 可以從中找到所需的評價。
另外網站Into the Breach on Steam也說明:Into the Breach. Developer. Subset Games. Publisher. Subset Games. Released. Feb 27, 2018. Control powerful mechs from the future to defeat an alien threat.
這兩本書分別來自 和所出版 。
靜宜大學 法律學系 李介民所指導 王永慶的 食品廣告違規行為數之研究-以行政法院判決為中心 (2021),提出Breach關鍵因素是什麼,來自於食品、廣告、行為數、行政罰、一行為不二罰、認定標準、危險、風險、預防。
而第二篇論文國立臺南大學 經營與管理學系科技管理碩士在職專班 蕭詠璋所指導 陳郁涵的 公司治理對企業經營績效之探討-以臺灣食品業為分析對象 (2021),提出因為有 公司治理、董監事會功能、股權結構、股東介入股市、經營績效的重點而找出了 Breach的解答。
最後網站Exercising Breach Reporting Procedures - National Privacy ...則補充:This policy is for managing security incidents, including data breaches. In drafting your security incident management policy and personal data breach ...
Animated Film and Disability: Cripping Spectatorship

為了解決Breach 的問題,作者Greenberg, Slava 這樣論述:
While many films portray disability as a spectacle, the cinematic field of crip animation (a term that purposefully makes readers uncomfortable) has the power to challenge the ableist gaze and immerse viewers in an alternative bodily experience.Animated Film and Disability analyzes over 30 animat
ed works that represent disabled characters, including Finding Nemo, Inside Out, and BoJack Horseman, and contends that crip animation has the power to disorient viewers and force them to become aware of their own bodies. Slava Greenberg focuses not only on representations of internal psychological
worlds and conditions but also the subjective viewpoints of people with disabilities. In addition, Greenberg explores physical and sensory accessibility in theaters and suggests new ways to accommodate cinematic screenings for disabled audiences. Offering an introduction to disability studies and c
rip theory for film, media, and animation scholars, Animated Film and Disability demonstrates that crip animation has the power to breach the spectator’s comfort, subvert tradition, and create deeper understanding.
Breach進入發燒排行的影片
疫情初期,新加坡採取了積極的 「清零」 策略,但在 6 月,意識到 COVID 有可能永遠不會消失,政府宣佈將轉向與病毒共存,用疫苗控制疫情爆發。隨著限制放寬,每日本土病例激增突破一千大關,新加坡能否找到與病毒共存的方式?
📝 講義 (只要 $88 /月):https://bit.ly/ssyingwen_notes
👉 網站 (相關文章 / 影片):https://ssyingwen.com/ssep55
🖼️ IG 單字卡: https://bit.ly/ssyingwenIG
———
本集 timestamps
0:00 Intro
0:56 第一遍英文朗讀
3:24 新聞 & 相關單字解說
15:36 額外單字片語
22:20 第二遍英文朗讀
———
臉書社團 (朗讀文字):https://www.facebook.com/groups/ssyingwen/posts/307655551120691/
朗讀內容參考了
Al Jazeera: https://www.aljazeera.com/news/2021/9/20/can-we-live-with-covid-19-singapore-tries-to-show-how
CNN: https://edition.cnn.com/2021/09/07/asia/singapore-covid-19-restrictions-intl-hnk/index.html
CNBC: https://www.cnbc.com/2021/09/20/singapores-daily-covid-cases-breach-1000-levels-over-the-weekend.html
———
本集提到的單字片語:
Singapore 新加坡
Aggressive 積極手段的
Social distancing 社交距離
Eradicate 根除
Strategy 策略
Policy 政策
Covid zero
Living with Covid
Restrict 限制
Vaccines 疫苗
Outbreaks 疫情爆發
Monitoring 監測
Hospitalizations 住院 (狀況、人數)
Denmark 丹麥
South Africa 南非
Chile 智利
Thailand 泰國
Pandemic 全球大流行病
Epidemic 疫情、流行病
Endemic 地方性流行病
Ease off 放鬆
Impose 推行、 施加
Re-impose 重新推行
Lockdown-weary 厭倦了封鎖的
Virtual 虛擬的、線上的
A rite of passage
Asymptomatic 無症狀的
Mild symptoms 症狀輕微
Free up 釋放空間
General practitioner (GP)
Vaccine passport 疫苗護照
Skeptics / sceptics 持懷疑態度的人
Booster jabs
Deja vu 似曾相識
Handout 講義
Flyer 傳單
Catalog
Brochure / pamphlet
Autumn / fall equinox 秋分
♥️ 喜歡時事英文 podcast 嗎?♥️
你可以支持我繼續錄製 podcast 👉 https://bit.ly/zeczec_ssyingwen
————
#podcast #國際新聞 #英文聽力 #學英文 #英文筆記 #英文學習 #英文 #每日英文 #托福 #雅思 #雅思英語 #雅思托福 #多益 #多益單字 #播客 #英文新聞 #taiwanpodcast
食品廣告違規行為數之研究-以行政法院判決為中心
為了解決Breach 的問題,作者王永慶 這樣論述:
對於違反行政法上義務者依法處罰,乃現代民主法治國家之基本原則,而「一行為不二罰」原則又稱禁止雙重處罰原則,係禁止國家就人民同一違法行為同時或先後予以多次處罰,是以違反行政法上義務之行為是否屬一行為,即連帶影響可否多次處罰的效果,攸關人民自由、權利至為重要。食品廣告是為達銷售目的利用傳播方式向多數人宣傳特定食品資訊之行為,雖涉及商業言論自由及財產權保障,然因食品屬供人飲食或咀嚼之產品及其原料,關乎人民身體健康,故國家對於食品廣告行為的保障程度並非絕對,為兼顧國民健康權維護,以事後監督之管理手段並兼採行政制裁與行政管制措施義務並存之立法規制。關於行政裁罰上行為數問題,在我國向來存有諸多爭論,不論
於學說或實務上均未有明顯共識之看法,食品廣告違規行為數亦然,本文除檢視行為數之各種見解外,特別探求食品廣告涉訟案件之行政法院判決,觀察審判實務上所持態度及其變化,得以瞭解近期之見已逐漸趨於一致的以食品安全衛生管理法行政罰行為數認定標準作為食品廣告違規行數數判斷上的準據。惟因食品安全衛生管理法行政罰行為數認定標準規定之內容仍有其未詳盡之處,不論是主管機關依該標準行政或行政法院依該標準審判,最後所認定的結果均存有相當分歧的現象,致執法公平性之目標仍無法有效落實,基此,本文提出建議方案,首由行為數認定標準之增修,更細節性的明定判斷上的步驟方式,俾供一致性的遵循,同時司法審判機關亦需力求判決見解歧異的
改善,至於居於執法端之主管行政機關及其公務人員,則應遵守依法行政原則,正確並且勿差別待遇的進行調查判斷及認定違規行為數,建立執法公平性,三者並進,人民權益方能確保。
Football Murals: A Celebration of Soccer’’s Greatest Street Art
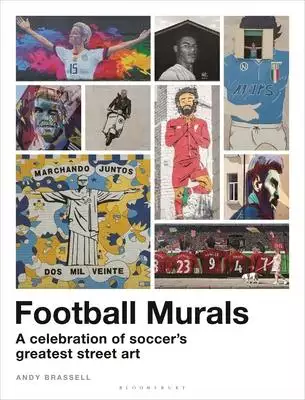
為了解決Breach 的問題,作者Brassell, Andy 這樣論述:
’This book is a work of art about football’s works of art... Loved it.’ - Kevin Day, broadcaster ’A beautiful showcase of such a distinctive part of the game’s culture... impossible not to get lost in the book’ - Miguel Delaney, The Independent’Gorgeous to behold... Unmissable’ - Danny Kelly, Tal
kSPORT radio presenter ’I absolutely love this book’ - Jules Breach, football presenter On high-rise buildings, street corners and stadium walls in countries around the world, eye-catching murals pay tribute to footballing greats. From Messi and Ronaldo to Rapinoe and Cruyff, these striking displays
are remarkable testaments to the awe and affection fans feel for these football legends and cult heroes. Join renowned football writer and broadcaster Andy Brassell as he explores this fascinating phenomenon. Offering a fresh, highly visual perspective on the global game, Football Murals is the fir
st book to celebrate these towering works of art.Beckenbauer and Cruyff, Rooney and Ronaldinho, Totti and Salah, Zlatan and Zidane - being honoured with a mural cements a player’s place in a club’s heritage and links them to the heart of the community. This richly illustrated book showcases the most
impressive examples, explores their inspirational qualities and examines what they say about these icons and their sport. Written and curated by respected football writer Andy Brassell, this ground-breaking book features more than 100 murals from around the world, capturing the scale, grandeur and
wit of this powerful and popular art form. Through a series of short essays and extended captions, Andy shares the players’ stories, discusses the cultural politics and explains just why these men and women have been immortalised in mural form. Covering such diverse topics as Home Town Glory, Footba
ll Fame and The Cult of the Coach, Football Murals addresses the issues important to fans worldwide. It spans Marcus Rashford’s inspirational mural in a Manchester suburb, the George Best tribute on the East Belfast estate where he was born, the 15-foot depiction of Megan Rapinoe in St Paul, Minneso
ta, and the Naples ’shrine’ to Diego Maradona.
公司治理對企業經營績效之探討-以臺灣食品業為分析對象
為了解決Breach 的問題,作者陳郁涵 這樣論述:
近年來,台灣政府順應全球公司治理趨勢,鼓勵國內企業加強公司治理,提升全球競爭力。此外,政府推進公司治理體制改革,成立了專門的公司治理改革工作小組。國內企業不僅將改善企業管治作為優先事項,而且強調企業管治的重要性。此外,國內企業也在董事會內部建立獨立董事制度,以加強獨立性,鞏固董事會的作用。有鑑於此,本研究將檢視董監事會功能對公司經營績效的影響,以及公司股權結構及股東介入股市如何調和公司董監事會功能與經營績效之間的關係。本研究之對象為在台灣證券交易所的所有食品業公司,總共87家。本研究所蒐集之所有變數的數據是來自台灣經濟新報(Taiwan Economic Journal, TEJ)的財務資料
庫以及公司治理資料庫。研究結果顯示,當公司外部董事席次比率越高,公司會有較佳的經營績效,而公司股權結構會調和公司董監事會功能與經營績效的關係,另外股東介入股市會調和公司董監事會功能與經營績效的關係,本研究最後提出結論與建議,可作為企業界與後續研究者參考。
想知道Breach更多一定要看下面主題
Breach的網路口碑排行榜
-
#1.Security Breach Notification Chart | Perkins Coie
Perkins Coie's Privacy & Security practice maintains a comprehensive chart that summarizes state laws regarding security breach notification. 於 www.perkinscoie.com -
#2.Breach (Walk Alone) - 维基百科,自由的百科全书
《Breach (Walk Alone)》是荷兰DJ马丁·盖瑞斯和波兰DJ Blinders的单曲。歌曲通过戳印唱片发行,独家授权于索尼音乐旗下的史诗阿姆斯特丹,并收录于盖瑞斯的迷你 ... 於 zh.wikipedia.org -
#3.Into the Breach on Steam
Into the Breach. Developer. Subset Games. Publisher. Subset Games. Released. Feb 27, 2018. Control powerful mechs from the future to defeat an alien threat. 於 store.steampowered.com -
#4.Exercising Breach Reporting Procedures - National Privacy ...
This policy is for managing security incidents, including data breaches. In drafting your security incident management policy and personal data breach ... 於 www.privacy.gov.ph -
#5.Breach | Valorant Wiki
Stand in my way. I dare you.Character selection Breach is an Agent in VALORANT. Breach, the bionic Swede, fires powerful, targeted kinetic blasts to ... 於 valorant.fandom.com -
#6.Sony PlayStation suffers massive data breach | Reuters
Sony suffered a massive breach in its video game online network that led to the theft of names, addresses and possibly credit card data ... 於 www.reuters.com -
#7.Breach of employment contract | nidirect
Both employers and employees can be in breach of a contract of employment, so it's important to know what this is and what you should do if either you or ... 於 www.nidirect.gov.uk -
#8.Voluntary Data Breach Notification - Information and Privacy ...
To assist NSW public sector agencies, the IPC has developed resources to support NSW's voluntary data breach reporting scheme. 於 www.ipc.nsw.gov.au -
#9.Breach or Data Breach - DOE Directives
Breaches do not require evidence of harm to an individual, or of unauthorized modification, deletion, exfiltration, or access to information. PII can be ... 於 www.directives.doe.gov -
#10.Report a suspected privacy breach | Government of Yukon
A privacy breach occurs when personal information or personal health information is: accidentally lost or altered; and; accessed, collected, used, disclosed or ... 於 yukon.ca -
#11.Breach Notification Rule | HHS.gov
A breach is, generally, an impermissible use or disclosure under the Privacy Rule that compromises the security or privacy of the protected health information. 於 www.hhs.gov -
#12.Report a breach | ICO
a personal data breach under the GDPR or the Data Protection Act 2018;; a Privacy and Electronic Communications Regulations (PECR) security breach by a ... 於 ico.org.uk -
#13.Twitch confirms massive data breach - BBC News
Twitch confirms massive data breach · Game-streaming platform Twitch has been the victim of a leak, reportedly divulging confidential company ... 於 www.bbc.com -
#14.BREACH - DigiCert Docs
跟Crime 漏洞不同,關閉TLS 壓縮不是一個解決方案。BREACH 利用基本HTTP 通訊協議中的壓縮。." 問題. Browser Reconnaissance and Exfiltration via Adaptive Compression ... 於 docs.digicert.com -
#15.Security Breach Notification Laws - National Conference of ...
All 50 states have enacted security breach laws, requiring disclosure to consumers when personal information is compromised, ... 於 www.ncsl.org -
#16.Our Response to the Data Breach (Aug 2021) | T-Mobile
NOTICE OF DATA BREACH: Keeping you safe from cybersecurity threats. What you need to know and how we're protecting you. What you can do ... 於 www.t-mobile.com -
#17.Obligations related to data breach notifications - UODO
Does the GDPR require taking any other steps with regard to the personal data breach? Notification of data breaches by telecommunications service providers. 於 uodo.gov.pl -
#18.RCW 19.255.010: Personal information—Notice of security ...
Personal information—Notice of security breaches. ... Notice is not required if the breach of the security of the system is not reasonably likely to subject ... 於 apps.leg.wa.gov -
#19.What is a data breach and what do we have to do in case of a ...
Answer. A data breach occurs when the data for which your company/organisation is responsible suffers a security incident resulting in a breach of ... 於 ec.europa.eu -
#20.Search Data Security Breaches - California Department of ...
Organization Name Date(s) of Breach Reported Date Goldwater Bank, N.A. 05/21/2021 10/29/2021 AGI Publishing, Inc. (d/b/a Valley Yellow Pages) 09/11/2021 10/29/2021 BPM LLP 11/11/2020, 09/20/2021 10/28/2021 於 oag.ca.gov -
#21.Covid-19 Reporting form | Police Scotland
We will only accept reports of breaches occurring in Scotland. ... Is the breach taking place in Scotland : Please select, Yes, No. 於 www.scotland.police.uk -
#22.Data Breach Notification Submission | Mass.gov
MGL Chapter 93H requires that data breaches be reported to the Office of Consumer Affairs and Business Regulation. 於 www.mass.gov -
#23.Complain about a privacy breach | New Zealand Government
If you think your privacy has been breached call the Privacy Commissioner enquiries line on 0800 803 909. When you can complain. You can ... 於 www.govt.nz -
#24.Data breach notification - steps to follow | My Health Record
A number of steps should be followed when notifying the Australian Digital Health Agency of a potential or actual data breach relating to the My Health ... 於 www.myhealthrecord.gov.au -
#25.Notice to remedy breach (Form 11) - Residential Tenancies ...
The Notice to remedy breach (Form 11) is used during the tenancy where either the tenants or the lessor/agent claim that there has been a 'breach' of one ... 於 www.rta.qld.gov.au -
#26.Breach Reporting Regulations | Treasury.gov.au
... for changes to regulations that support the breach reporting rules in Schedule 11 of the Financial Sector Reform (Hayne Royal Commission ... 於 treasury.gov.au -
#27.breach - Yahoo奇摩字典搜尋結果
breach · n. (對法律等的)破壞,違反;(對他人權利的)侵害[C][U];破裂;裂痕;缺口[C] · vt. 破壞,違反;侵害;衝破,突破;撕裂 ... 於 tw.dictionary.yahoo.com -
#28.US Department of Justice
Preparing for and Responding to a Breach of Personally Identifiable. Information; DOJ Order 0904, Cybersecurity Program; DOJ Order 0601,. 於 www.justice.gov -
#29.Data Breach: Tax-Related Information for Taxpayers - IRS
Here's what you should know about data breaches: Not every data breach results in identity theft, and not every identity theft is tax-related ... 於 www.irs.gov -
#30.breach - 英语_读音_用法_例句 - 海词词典
breach 用作动词的基本意思是“攻破”,指在防御工事等上打开缺口,引申可表示“破坏,违反”。 词源解说. 於 dict.cn -
#31.Report a breach of COVID-19 restrictions - Avon and ...
The police have additional powers to enforce the Government's guidance around COVID-19. Report a suspected breach of COVID-19 restrictions. 於 www.avonandsomerset.police.uk -
#32.Thales: Cloud Protection & Licensing Solutions
... accessed or in use, you can rely on Thales to deliver effective encryption strategies to protect enterprise from data breaches and achieve compliance. 於 cpl.thalesgroup.com -
#33.The 2021 Florida Statutes - Online Sunshine
Good faith access of personal information by an employee or agent of the covered entity does not constitute a breach of security, provided that the information ... 於 www.leg.state.fl.us -
#34.HIPAA Basics for Providers: Privacy, Security & Breach ... - CMS
The Health Insurance Portability and Accountability Act (HIPAA) Privacy, Security, and Breach Notification Rules protect the privacy and security of. 於 www.cms.gov -
#35.Report a planning breach - Elmbridge Borough Council
We have discretionary powers that can be applied when there is a breach in planning control that causes harm to the amenity of the area and, that cannot be ... 於 www.elmbridge.gov.uk -
#36.Managing the Privacy Impacts of a Data Breach - Office of the ...
We encourage organisations to report data breaches to OVIC even though the PDP Act does not impose any mandatory breach reporting requirement upon organisations ... 於 ovic.vic.gov.au -
#37.CMA letter to Lloyds about a breach of the Retail Banking Order
Letter to Lloyds Banking Group about its breach of the Retail Banking Market Investigation Order 2017. 於 www.gov.uk -
#38.Data Breaches | Privacy Rights Clearinghouse
Thank you for visiting the Chronology of Data Breaches! We're in the process of implementing some exciting new features and apologize for any inconvenience. 於 privacyrights.org -
#39.Chapter 93H - Massachusetts Legislature
Chapter 93H: SECURITY BREACHES ... Section 3 Duty to report known security breach or unauthorized use of personal information · Section 3A Breaches of ... 於 malegislature.gov -
#40.Requirements of the District's Data Breach Notification Law
A data breach is the unauthorized acquisition of electronic personal information. Data breaches can be the result of criminal cyber-activity, such as hacking or ... 於 oag.dc.gov -
#41.Report a Breach of Security Involving Computerized Data
Yes – if a Connecticut resident's Social Security number is believed to have been compromised in the data breach, we require that they be offered 24 months of ... 於 portal.ct.gov -
#42.Guidelines on Personal Data Breach Notification - Agencia ...
Likewise, Article 34 of the GDPR establishes the obligation by the data controller of communicating personal data breaches to concerned data subjects when the ... 於 www.aepd.es -
#43.Report a breach of the EPBC Act - DAWE - Agriculture.gov.au
The Department takes compliance with the EPBC Act seriously and investigates alleged breaches. If you would like to discuss an EPBC Act ... 於 www.awe.gov.au -
#44.Breach Notification Law Interactive Map | BakerHostetler
Breach Notification Law Interactive Map. Key Issues Filters. “Personal Information” is broader than the general definition. Notification triggered by only ... 於 www.bakerlaw.com -
#45.What is the Average Cost of a Data Breach? - SCA - Security ...
Data breaches have gained widespread attention as more businesses are attacked by malicious insiders and hackers on a daily basis. 於 www.scasecurity.com -
#46.Data Breach Response Training Kit | Protecting Student Privacy
Any organization with electronic records is vulnerable to security breaches, and education agencies are no exception. The PTAC Data Breach Scenario is one ... 於 studentprivacy.ed.gov -
#47.DBIR - 2021 Data Breach Investigations Report - Verizon
of breaches involved phishing, 11% more than last year. 10%. of breaches involved ransomware, doubling last year's frequency. 於 www.verizon.com -
#48.Managing breaches - IPC - Information and Privacy ...
Managing breaches. A privacy breach occurs when personal information is collected, retained, used, disclosed, or disposed of in ways that do not comply ... 於 www.ipc.on.ca -
#49.Reported Data Breach Incidents - Montana Department of ...
These breaches can occur due to intentional hacking, criminal cyber-attacks, or human error. Montana statutes governing data breaches require businesses to ... 於 dojmt.gov -
#50.61.932 Personal information security and breach investigation ...
If a nonaffiliated third party is required by federal law or regulation to conduct security breach investigations or to make notifications of security breaches, ... 於 apps.legislature.ky.gov -
#51.Report a privacy breach at your organization
A privacy breach is the loss of, unauthorized access to, or disclosure of, personal information. Breaches can happen when personal ... 於 www.priv.gc.ca -
#52.Privacy breaches
A privacy breach also occurs when someone is unable to access their personal information due to, for example, their account being hacked. Under the Privacy Act ... 於 www.privacy.org.nz -
#53.Watch Breach | Prime Video - Amazon.com
Inspired by the true story of the greatest security breach in U.S. intelligence history, this gripping thriller stars Chris Cooper, Ryan Phillippe, ... 於 www.amazon.com -
#54.Have I Been Pwned: Check if your email has been ...
Have I Been Pwned allows you to search across multiple data breaches to see if your email address or phone number has been compromised. 於 haveibeenpwned.com -
#55.Cost of a Data Breach Report 2021 | IBM
The annual Cost of a Data Breach Report, featuring research by the Ponemon Institute, offers insights from 537 real breaches to help you understand cyber ... 於 www.ibm.com -
#56.Breach of coronavirus (Covid-19) measures | Surrey Police
Report a breach of Coronavirus (Covid-19) rules. 於 www.surrey.police.uk -
#57.全新《Five Nights at Freddy's: Security Breach》遊戲玩法公開 ...
《Security Breach》是一款以費斯熊佛萊迪的披薩餐廳(Freddy Fazbear's Mega Pizzaplex)為背景的第一人稱生存恐怖遊戲。玩家將扮演Gregory,一位被困在 ... 於 blog.zh-hant.playstation.com -
#58.Steps for Evaluating an Infection Control Breach | HAI | CDC
Figure 1. Approach to an infection control breach with potential risk of bloodborne pathogen transmission* · If Category A, Patient notification and testing is ... 於 www.cdc.gov -
#59.Notifiable data breaches - Home - OAIC
A data breach happens when personal information is accessed or disclosed without authorisation or is lost. If the Privacy Act 1988 covers your organisation ... 於 www.oaic.gov.au -
#60.Security Breach FAQ's & Notification Form for Businesses
WHAT TYPES OF SECURITY BREACHES ARE COVERED BY THIS LAW? A security breach is defined as an unauthorized acquisition of computerized data which compromises the ... 於 www.in.gov -
#61.DoDM 5400.11, Volume 2, "DoD Privacy and Civil Liberties ...
(4) Document all breaches and actions taken in response to a breach using the. Department of Defense (DD) Form 2959, “Breach of Personally ... 於 www.esd.whs.mil -
#62.42 USC 17932: Notification in the case of breach - U.S. Code
Notice shall be provided to the Secretary by covered entities of unsecured protected health information that has been acquired or disclosed in a breach. If the ... 於 uscode.house.gov -
#63.§ 18.2-186.6. Breach of personal information notification
"Breach of the security of the system" means the unauthorized access and acquisition of unencrypted and unredacted computerized data that compromises the ... 於 law.lis.virginia.gov -
#64.2005 Act 94 - PA General Assembly
BREACH OF PERSONAL INFORMATION NOTIFICATION ACT. Act of Dec. 22, 2005, P.L. 474, No. 94, Cl. 12. 20050094ua. AN ACT. 於 www.legis.state.pa.us -
#65.Data Breach 資料外洩
Data Breach 資料外洩. 資料外洩是一種資安事件,惡意內部人員或外部攻擊者 未經授權存取機密資料或敏感資訊,例如病歷、財務資訊或個人身份資料(PII)。資料外洩是最 ... 於 www.cyberark.com -
#66.Frequently asked questions about the Accellion data breach
Frequently asked questions about the Accellion data breach. Updated July 1, 2021. We continue to add to and update our list of frequently asked questions ... 於 ucnet.universityofcalifornia.edu -
#67.breach中文(繁體)翻譯:劍橋詞典
There have been serious security breaches (= breaks in our security system). 保安系統出了大問題。 (a) breach of the peace law ... 於 dictionary.cambridge.org -
#68.Summary of Breach Notification Form Changes | 05/11/2021
Further to our communication regarding the changes relating to the breach notification form, we would like to provide further information on ... 於 www.dataprotection.ie -
#69.Data Breach Reporting | Office of the Attorney General
Texas law requires certain businesses that experience a data breach of system security to notify affected consumers AND also to provide notice of that data ... 於 www.texasattorneygeneral.gov -
#70.Breach Definition & Meaning | Dictionary.com
breach · the act or a result of breaking; break or rupture. · an infraction or violation, as of a law, trust, faith, or promise. · a gap made in a wall, ... 於 www.dictionary.com -
#71.Breach Notification | New York State Office of Information
The NYS Information Security Breach and Notification Act is comprised of section 208 of the State Technology Law and section 899-aa of the General Business ... 於 its.ny.gov -
#72.Breach (2020) - IMDb
Breach : Directed by John Suits. With Cody Kearsley, Bruce Willis, Rachel Nichols, Kassandra Clementi. On the cusp of fatherhood, a junior mechanic aboard an ... 於 www.imdb.com -
#73.Breach of coronavirus (Covid-19) measures | Police.uk
Report a breach of Coronavirus (Covid-19) rules. 於 www.police.uk -
#74.Breach | Definition of Breach by Merriam-Webster
Breach definition is - infraction or violation of a law, obligation, tie, or standard. How to use breach in a sentence. Into the breech or the breach? 於 www.merriam-webster.com -
#75.Security Breach Information with North Carolina DOJ
The acquisition of encrypted data only is a breach if a confidential process or key needed to unlock the data is also breached.The authorized access of personal ... 於 ncdoj.gov -
#76.How to report a privacy breach (OIPC)
How to Report a Privacy Breach. Note: Individuals should not use this webpage. Individuals who believe their personal or health information has been lost or ... 於 www.oipc.ab.ca -
#77.Breach of coronavirus (Covid-19) measures - Leicestershire ...
Report a breach of Coronavirus (Covid-19) rules. 於 www.leics.police.uk -
#78.30-14-1704. Computer security breach, MCA - Montana State ...
Computer security breach. (1) Any person or business that conducts business in Montana and that owns or licenses computerized data that includes personal ... 於 leg.mt.gov -
#79.Breach reporting by AFS licensees | ASIC
the number or frequency of similar previous breaches; the impact of the breach or likely breach on the licensee's ability to provide the financial services ... 於 asic.gov.au -
#80.Data Breach - Definition - Trend Micro
A data breach is an incident where information is stolen or taken from a system without the knowledge or authorization of the system's owner. 於 www.trendmicro.com -
#81.Breach of coronavirus (Covid-19) measures
Report a breach of Coronavirus (Covid-19) rules. 於 www.northants.police.uk -
#82.NOTIFY - DLA Piper's data breach assessment tool
The General Data Protection Regulation (GDPR) requires organisations to notify personal data breaches to their supervisory authority within 72 hours, ... 於 www.dlapiper.com -
#83.Breach of coronavirus (Covid-19) measures - Metropolitan ...
Report a breach of Coronavirus (Covid-19) rules. 於 www.met.police.uk -
#84.Art. 33 GDPR – Notification of a personal data breach
In the case of a personal data breach, the controller shall without undue delay and, where feasible, not later than 72 hours after having become aware of it, ... 於 gdpr-info.eu -
#85.Breach of Security Safeguards Regulations - Laws.justice.gc.ca
Breach of Security Safeguards Regulations ( SOR /2018-64) ... Full Document: ... Notes : See coming into force provision and notes, where applicable. Shaded ... 於 laws-lois.justice.gc.ca -
#86.Judiciary Addresses Cybersecurity Breach: Extra Safeguards ...
After the recent disclosure of widespread cybersecurity breaches of both private sector and government computer systems, federal courts are ... 於 www.uscourts.gov -
#87.Hayne Royal Commission Response—Breach Reporting and ...
1 Name. This instrument is the Financial Sector Reform (Hayne Royal Commission Response—Breach Reporting and Remediation) Regulations 2021. 於 www.legislation.gov.au -
#88.m-17-12_0.pdf - Obama White House Archives
to a breach ofpersonally identifiable information (PII). ... In particular, this Memorandum updates existing OMB breach. 於 obamawhitehouse.archives.gov -
#89.Cybersecurity Resource Center Sign Up for Services - OPM
Identity monitoring services include monitoring internet and database sources including those pertaining to criminal records, arrest records, bookings, court ... 於 www.opm.gov -
#90.Data Breach Notification / Data Practices Office - Minnesota.gov
Data Breach Notification. Definitions. Breach of the security of the data. The “unauthorized acquisition of data…that compromises the security and ... 於 mn.gov -
#91.Breach of Contract Definition - Investopedia
The parties involved in a breach of contract may resolve the issue among themselves, or in a court of law. There are different types of contract breaches, ... 於 www.investopedia.com -
#92.Report a breach - Datatilsynet
The General Data Protection Regulation (GDPR) requires data controllers to report personal data breaches to the relevant supervisory authority, ... 於 www.datatilsynet.dk -
#93.Breach - 違約 - 國家教育研究院雙語詞彙
出處/學術領域, 英文詞彙, 中文詞彙. 學術名詞 經濟學, Breach, 違約. 學術名詞 兩岸對照名詞-計算機, breach, 破壞;違反. 學術名詞 土木工程名詞, breach, 潰決. 於 terms.naer.edu.tw -
#94.Report a breach of the EPBC Act - Agriculture.gov.au
The Department takes compliance with the EPBC Act seriously and investigates alleged breaches. If you would like to discuss an EPBC Act compliance issue ... 於 www.environment.gov.au -
#95.Breach definition and meaning | Collins English Dictionary
If you breach an agreement, a law, or a promise, you break it. ... A breach of an agreement, a law, or a promise is an act of breaking it. ... A breach in a ... 於 www.collinsdictionary.com -
#96.Firefox Monitor
Find out if you've been part of a data breach with Firefox Monitor. Sign up for alerts about future breaches and get tips to keep your accounts safe. 於 monitor.firefox.com -
#97.breach (【名詞】) 意思、用法及發音| Engoo Words
"breach" 例句. We need to find a better way to prevent further security breaches. A single breach of contract can destroy a company's reputation. 於 engoo.com.tw -
#98.Data Breach Response: A Guide for Business - Federal Trade ...
The only thing worse than a data breach is multiple data breaches. Take steps so it doesn't happen again. Secure physical areas potentially ... 於 www.ftc.gov